I’ve been able to get a full end-to-end test of this, this is awesome, thanks Lukas! Here’s how I got it working:
Libvirt
If you’re not testing on hardware, a great way to test this is using UEFI firmware on a QEMU vm. There’s a package called edk2-ovmf you can use. On Fedora, it’s got the latest and greatest. If you are on CentOS 7 or want to use the latest nightlies, you can get them from this fedora documentation. They don’t seem to have TLS support, which means you can’t enroll a TLS certificate to make HTTPS boot work. The Fedora 28 firmware does seem to support this.
On CentOS 7 only (Fedora already knows the paths), after installing the firmware package, you’ll also need to configure the nvram setting ini /etc/libvirt/qemu.conf:
nvram = [
"/usr/share/edk2.git/ovmf-x64/OVMF_CODE-pure-efi.fd:/usr/share/edk2.git/ovmf-x64/OVMF_VARS-pure-efi.fd"
]
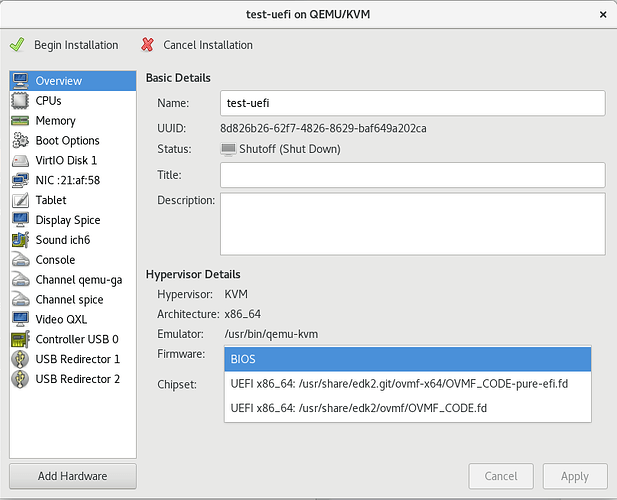
Once you do that, you can create an UEFI vm, by selecting the UEFI x86_64 firmware:
Foreman
You’ll need Lukas’ two PR’s above.
Configure the smart-proxy with the httpboot plugin, setting the directory to /var/lib/tftpboot. You’ll need a symlink for the boot directory:
ln -s /var/lib/tftpboot/boot /var/lib/tftpboot/grub2/boot
There’s an installer PR for this:
Once you’ve got that setup, create a Foreman host, and set the PXE loader to Grub2 UEFI HTTP. Power on the VM. Note: you’ll need to create the VM manually, as foreman automatically creates libvirt VM’s with BIOS.
grub2
Unfortunately the fully working grub2 won’t be in until Fedora 29 or CentOS 7.6 (at the earliest). But, you can build your own.
Checkout Prepend prefix when HTTP path is relative by stbenjam · Pull Request #29 · rhboot/grub2 · GitHub, and let’s build it:
$ mkdir /tmp/grub
$ ./autogen.sh
$ ./configure --with-platform=efi --target=x86_64 --disable-werror --prefix=/tmp/grub
$ make && make install
$ /tmp/grub/bin/grub-mkimage -O x86_64-efi -o grubx64.efi -p /EFI/centos -d /tmp/grub/lib/grub/x86_64-efi all_video boot btrfs cat chain configfile echo efifwsetup efinet ext2 fat font gfxmenu gfxterm gzio halt hfsplus iso9660 jpeg loadenv lvm mdraid09 mdraid1x minicmd normal part_apple part_msdos part_gpt password_pbkdf2 png reboot search search_fs_uuid search_fs_file search_label sleep syslinuxcfg test tftp regexp video xfs linuxefi multiboot2 multiboot
Put the resulting grubx64.efi into your /var/lib/tftpboot/grub2 directory.