Problem:
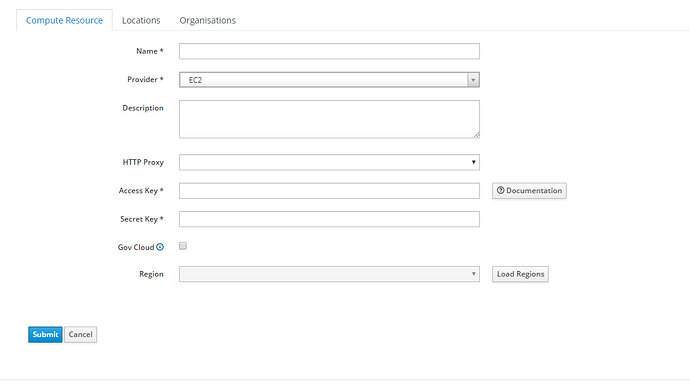
Currently we have an EC2-instance on AWS running, on which Foreman and puppetserver are installed. When adding compute resources for AWS, we are requested to fill in an access key/secret key (see screenshot below):
However for security reasons, we are not allowed to use access / secret keys (as they could be leaked), but are required to use IAM roles assigned to the EC2-instance for authentication.
The AWS tools (Cloudformation, CDK, …) support authentication via IAM role assigned to the EC2 instances.
Is a similar authentication available / scheduled to be availbe in Foreman? Is there a work around to avoid using access /secret keys. Currently the access key/secret key are required to be filled in
Expected outcome:
Being able to create EC2 instances with Foreman, without having to rely on access/secret keys
Foreman and Proxy versions:1.22.0-1.el7
Foreman and Proxy plugin versions:foreman-ec2 (1.22.0-1.el7)
Hi,
I’ve been searching a bit, and it seems this could be solved by using the following parameter in the fog connector: use_iam_profile = true;
I haven’t searched yet how it works in the foreman code itself though. 
related ticket @fog: https://github.com/fog/fog-aws/issues/441
Bert
IAM role can set be per instance on image level, at least that’s what I understand from Feature #2229: Support IAM roles when provisioning via EC2 - Foreman
Try editting image in your compute resource detail page and set the IAM role there. It would be good to hear whether it works. Then it’s easy to improve our docs.
Another question would be, if it makes sense to store per image, or it should rather be configurable per compute profile or other entity.
Hi Bert
Thank you for your useful input
As a current workaround we edited some ruby code on the server:
/usr/share/foreman/app/models/compute_resources/foreman/model/ec2.rb:
replace
@client ||= ::Fog::Compute.new(:provider => "AWS", :aws_access_key_id => user, :aws_secret_access_key => password, :region => region, :connection_options => connection_options)
by
@client ||= ::Fog::Compute.new(:provider => "AWS", :use_iam_profile => true, :region => region, :connection_options => connection_options)
This way we are able to create and launch instances in a more secure way.
Benonie
1 Like